CITIC Securities Company Limited (hereinafter referred to as “CITIC Securities”, or the “Company”) deeply recognizes the materiality of corporate data security and personal information protection for the financial services industry, and regards it as the core cornerstone of the Company's compliance operation. In order to effectively protect the legitimate rights and interests of customers and regulate the entire process of data processing, the Company issues this statement in accordance with laws and regulations such as the Securities Law of the People's Republic of China, the Cybersecurity Law of the People's Republic of China, the Data Security Law of the People's Republic of China, the Personal Information Protection Law of the People's Republic of China, and the Measures for the Information Technology Management of Securities Fund Operators.
I.Organizational structure and management system
The Company has established a three-level digital organization structure of "decision-making level, management level and execution level":
• Decision-making level: The Company's digitization committee, as the leading and highest deliberative body of the Company's digitization work, is responsible for the Company's data governance, digitization operation and management, information technology governance and network and information security.
• Management level: A special working group is set up under the digitization committee, responsible for formulating management systems related to data governance, data security protection and personal information protection of the Company, coordinating and promoting various departments to carry out various work, and improving the level of data security governance.
• Execution level: An execution system composed of the Information Technology Center, Compliance Department, and various business lines, ensures the effective implementation of management requirements throughout the entire business process.
The Company has established a company level data security and personal information protection system applicable to all employees in various departments, business lines, and branch offices, including the Management Measures for Data Governance of CITIC Securities Company Limited, Management Measures for Personal Information Protection of CITIC Securities Company Limited, Management Measures for Cybersecurity of CITIC Securities Company Limited, and the accompanying management and implementation rules, which cover all business systems, data assets and information. The scope of management covers all business systems, data assets and information processing activities of the Company.
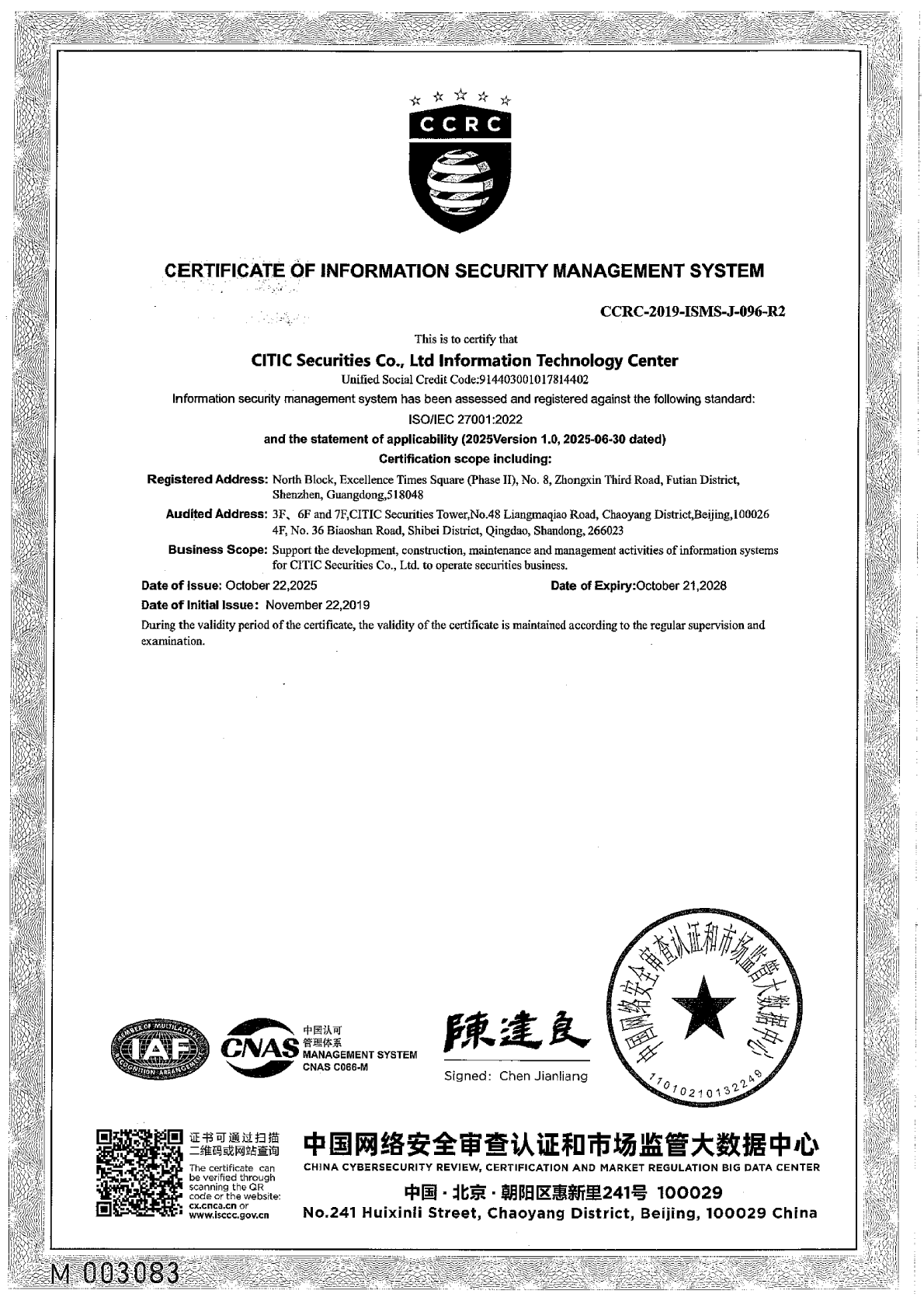
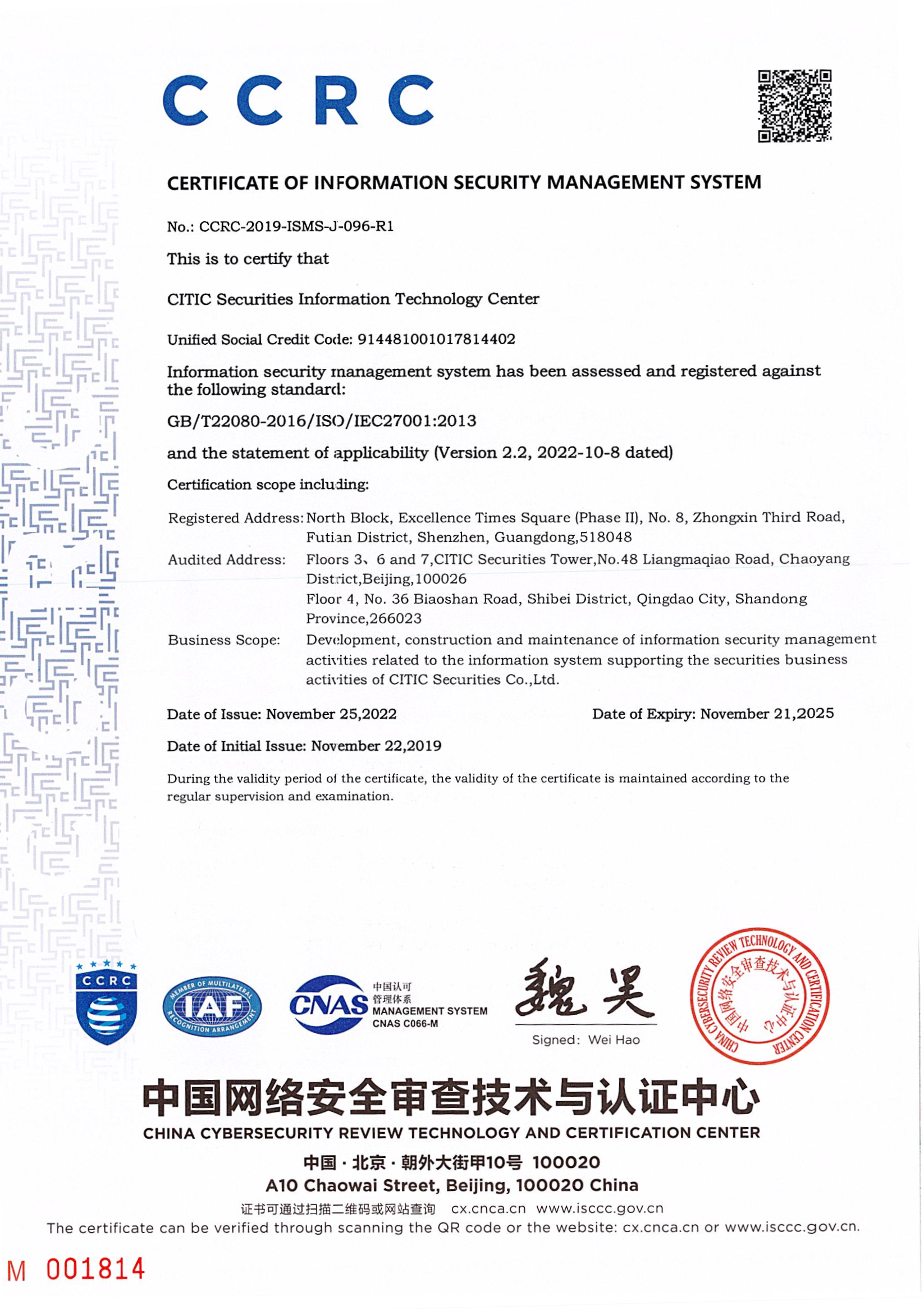
The Company has passed the certification of ISO 27001 Information Security Management System criteria, and all systems have completed the grading and evaluation work in accordance with the national network security level protection requirements.
II.Protection of personal information rights and interests
The Company fully guarantees the rights and interests of customer information subjects, and promises to take corresponding security measures to protect customer personal information in accordance with national personal information protection requirements, and provide convenient channels for exercising rights and interests:
i. Collection principles
The Company strictly follows the principle of "clear purpose and minimum necessity" to collect customer data, and only collects customer information that is directly related to the provision and handling of securities business services.
ii. Personal consent principle
The Company publishes privacy protection agreements to customers through apps, web pages, and other means, clearly informing customers of the purpose, processing method, type of personal information processed, and storage period of personal information, and collecting and processing customer personal information with their consent.
iii. Right of access
The Company discloses personal information processing rules through privacy protection clauses and can check the list of collected personal information.
iv. Right of rectification
When customers discover errors in information, they can apply for correction through online and offline channels, and the Company will complete the verification and processing within 3 working days.
V. Right of cancellation/deletion
The Company provides a one-stop service for account cancellation. After the customer cancels their internet account, the Company will promptly clear their internet account information. After the customer cancels their fund account, the Company will no longer collect personal information related to the account; If the customer withdraws the information processing authorization, the Company shall immediately cease the activity of continuing to collect the customer's personal information.
VI. Data processing specifications
The Company promises not to rent, sell or provide personal data to third parties for purposes other than completing transactions/services.
III.Data security protection measures
i. Data lifecycle protection measures
The Company carries out data classification and classification protection work, based on data security protection level, carries out information system construction and data lifecycle protection, and protects customer personal information and data security by comprehensively utilizing various data security protection tools such as data desensitization, data backup, and terminal spill prevention.
The Company has established a deep defense system for network and data security, deploying intrusion detection tools and security protection tools at the network layer, host layer, and application layer respectively; Implement strict network host application resource application and release management mechanisms; Establish the ability to audit data operation behavior, properly store various operation behavior logs, and achieve audit traceability of internal and external data access behavior.
The Company conducts practical network security attack and defense drills, tests employees' awareness of network security protection, and verifies the information system network and data security protection capabilities.
ii. Permission control
The Company controls data access permissions according to the management requirements of "minimizing job adaptation permissions", and employees can only obtain the necessary data permissions to complete their job duties; the Company establish an access permission application and approval mechanism for important information systems, and adjust and clear access permissions based on employee identity.
iii. Third party management
The Company's requirements and measures for data and information protection cover all supplier and business partners, implement strict access management, sign data security protection agreements, clarify data processing boundaries and responsibilities.
iv. Emergency response mechanism
In response to typical security incidents such as personal information leakage and data unavailability, the Company has formulated an emergency disposal plan for information system data security incidents, and standardized the response methods for data security incident monitoring, problem positioning, emergency disposal, root cause analysis, event handling, subsequent optimization, and event reporting.
V. Employee training
The Company conducts annual training on network security and data security protection for all employees, enhancing their awareness of security protection responsibilities and enhancing their basic skills in preventing phishing emails, network attacks, and data security breaches.
IV.Supervision and incentive mechanism
i. Information security audit
The Company conducts an external information technology audit once a year and a comprehensive information technology audit every three years. The audit scope covers information technology governance, risk compliance management, information system security, operation and maintenance management, computer room management, data management, emergency management, information technology service organization management.
ii. Information security supervision mechanism
The relevant senior executive of the Company take the responsibility of privacy and data security and supervise the personal information processing activities and the protective measures taken.
The Company adheres to the principle of "whoever handles is responsible" and clarifies the department responsible for personal information processing as the first person responsible for personal information processing.
iii. Safety responsibility system
The Company strictly implements the network responsibility system, including the responsibility for network and data security protection in the comprehensive assessment of employees. If a security incident occurs, relevant personnel will be held accountable.
iv. Continuous optimization
Establish a customer feedback mechanism, collect information protection related suggestions through customer service hotlines, suggestion boxes, and other channels, timely update personal information protection clauses and regularly update data security management systems, introduce cutting-edge security technologies, and continuously improve protection capabilities.